North Korean (DPRK) IT workers are ramping up their corporate infiltration efforts into tech and crypto firms, with a focus on Europe.
Since its last report in September 2024, Google Threat Intelligence Group has observed a rise in DPRK IT workers infiltrating tech and crypto firms in multiple countries across Europe. These individuals use fake identities and create multiple fake personas to secure high-paying jobs at tech and blockchain companies, often using additional fabricated personas for references. In one case, a single individual was found operating under at least 12 different personas across Europe and the U.S., targeting organizations within the defense and government sectors.
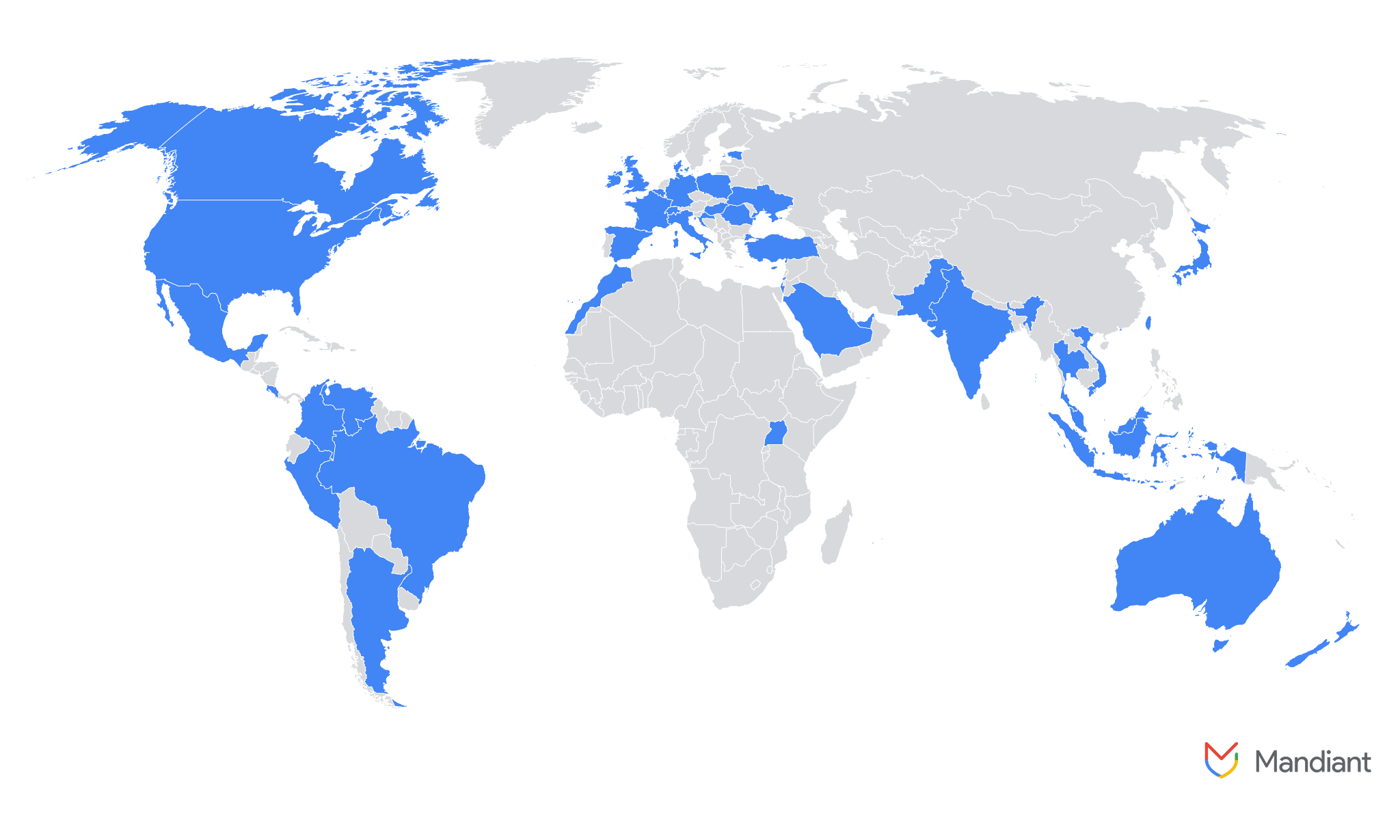 Source: List of countries impacted by DPRK IT workers
Source: List of countries impacted by DPRK IT workersAccording to the latest report, a number of of DPRK IT workers have been found to be actively involved in blockchain projects in the UK, such as developing Solana and Anchor/Rust smart contracts and building a blockchain-based job marketplace using the MERN stack and Solana.
In addition to the IT workers themselves, investigations have also uncovered a network of facilitators supporting these workers in navigating European job websites and providing them with false identity documents.
North Korea’s aggressive expansion of IT worker infiltration is largely driven by the regime’s need to circumvent international sanctions that have restricted its access to global financial systems. With economic pressure mounting, the country has turned to cyber operations as a major revenue stream, using IT workers to secure high-paying jobs and funnel earnings back to the state. In 2022, the U.S. Treasury Department estimated that these workers collectively generate hundreds of millions of dollars annually for North Korea. The DPRK government withholds up to 90 percent of the wages earned by these workers, thereby channeling substantial funds into its military projects.
Beyond directly funneling their salaries to the regime, North Korean IT workers sometimes act as entry points for state-sponsored hacking groups like Lazarus Group, which was recently in the spotlight for orchestrating the $1,5 billion hack of Bybit exchange. Notably, Lazarus stole over $600 million from the Ronin Network (Axie Infinity) in 2022, with IT workers playing a key role in providing access to internal systems. In August 2024, on-chain sleuth ZachXBT uncovered over 25 crypto projects infiltrated by DPRK devs.
While Lazarus’s hack of Bybit—after which North Korea became the fifth-largest government holder of Bitcoin (BTC)—was linked to the exploitation of vulnerabilities in its multi-sig wallet rather than direct infiltration, it has raised awareness of the DPRK’s threat in the U.S. According to GTIG report, this heightened awareness is one of the key factors behind the expansion of North Korean infiltration efforts into Europe, in addition to increased public reporting, U.S. Department of Justice indictments, and challenges related to right-to-work verification.














 English (US) ·
English (US) ·